Last Updated on October 10, 2024 by Team TBH
Ransomware is seen as one of the most dangerous cybersecurity threats today and has become a significant issue for individuals, corporate bodies, and government organizations. Given the increasingly sophisticated tactics embraced in ransomware attacks by cyber criminals, the need for accurate detection to prevent such acts of extortion has never been so urgent.
In this detailed article, we will explore what ransomware is, explain how ransomware works, and the signs of a ransomware infection. Finally, it briefly discusses measures that can be taken to prevent perpetrators of such attacks. Increased awareness and strengthened security practices can be valuable in preventing the catastrophic effects of ransomware infections for interested parties.
Understanding Ransomware
Ransomware is malware that encrypts files on a victim’s device and demands pay for its release, with the threat of destruction or denial of access if a ransom is not paid. Attackers tend to demand a ransom in crypto, as that can make the tracing and reclaim process hard. Ransomware is a menace that threatens not only badly trained or uninformed end users but can collapse businesses under financial loss and ruin the reputations of both organizations and citizens they have hacked.
Ransomware is one of the most feared cybersecurity threats today, and for good reason: it has the potential to bring business operations to a grinding halt while exposing confidential data. Ransomware has become an increasing threat in a more digital world, and understanding how it works is the first part of ensuring we have some mechanisms to deal with ransomware.
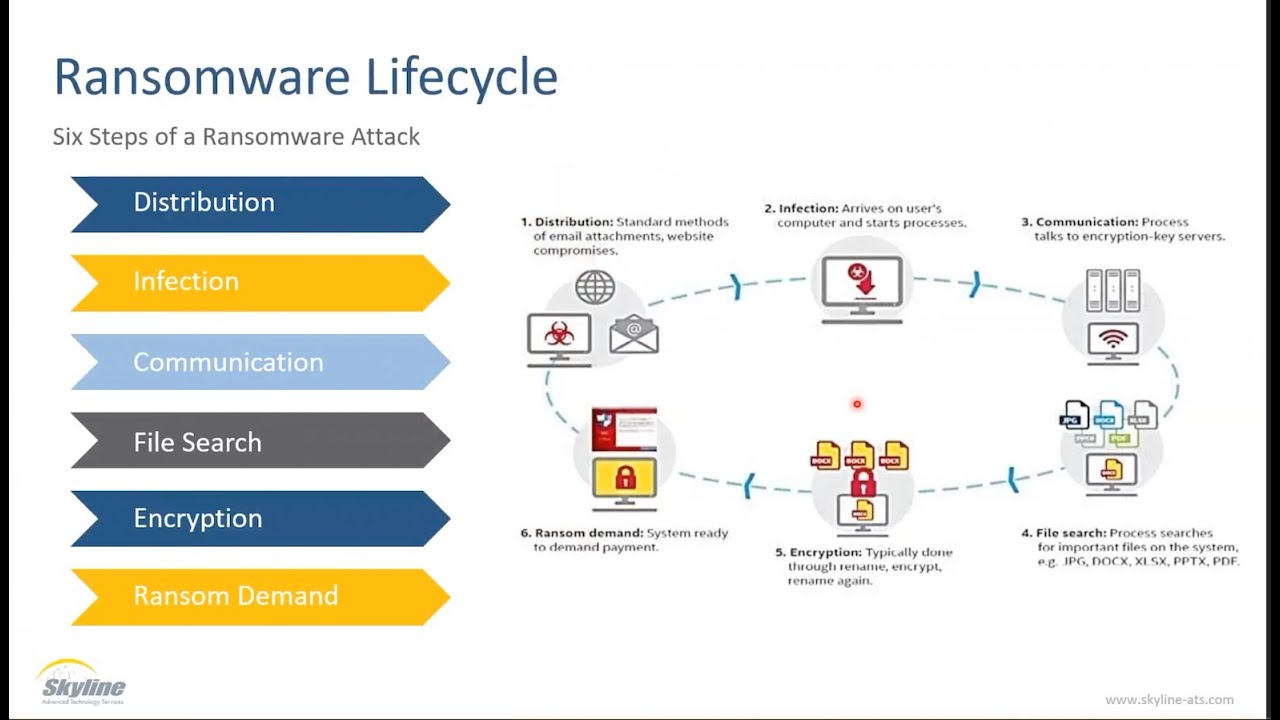
The Ransomware Lifecycle
To indeed detect ransomware, you must understand its lifecycle which usually involves the following:
- Infection: Ransomware is most efficiently spread through phishing emails, malicious attachments, or compromised websites. Users can quickly address this.
- Execution: Like other ransomware, the application can stay hidden until it’s time to run its true purposes, making it very hard for us, even tech-savvy individuals, to identify the threat early.
- Encryption: Ransomware encrypts categories of files, usually critical data such as documents, images, and databases.
- Demand for Ransom: The attacker posts a ransom note containing instructions on how to pay (often with a specific, time-limited window during which the money must be sent).
- Post-Attack: If you pay the ransom, there is no guarantee that your files will be returned to you or that the attackers won’t return for more.
Early Warning Signs
Here are the tips on recognizing that in the early stages of a ransomware attack, which could save you from full-blown encryption. These are things you should look for to know:
1. Unusual System Behavior
Sudden system slowness, applications suddenly unresponsive, or files behaving abnormally could be signs of a ransomware infection. Pay attention to:
- Increased CPU usage: Ransomware typically takes system resources during encryption.
- File renaming: Another expected behavior is for ransomware to work by taking the files and changing their shape or file extension; once ransomware questions are found, your data volume is inoperable.
2. Suspicious Network Activity
You can also observe the network packets that will be incoming over your network if you get traffic in a very high range and, thus, diagnose any ransomware in it. Look for:
- Unusual outbound traffic: Connections to unknown IP addresses that involve large data exchanges may point to unauthorized access.
- Multiple failed login attempts: This may indicate a brute force attack and the initial methods ransomware attackers use to get their foot in the door.
3. Alerts from Security Software
Recent security solutions have used Behavioral and heuristic analysis to detect outliers. Pay attention to:
- Ransomware-specific alerts: A lot of security systems have been developed with the capability to detect both known signature ransomware and strange file changes.
- Blocked processes: The antivirus or endpoint protection software has blocked a process.
Tools for Ransomware Detection
Many techniques and tools can be useful in improving the ransomware detection:
1. Intrusion Detection Systems (IDS)
IDS is designed to detect any suspicious activity or policy violations in network traffic. This way, it creates admin alerts on possible ransomware activity at an early stage.
2. Endpoint Detection and Response (EDR)
EDR solutions to monitor how these devices behave at the endpoint level, determine when a device may be acting suspiciously, and then responding real time based on that information. They can also identify the infected systems and quarantine devices to eliminate further proliferation.
3. Security Information and Event Management (SIEM)
SIEM solutions use this data to detect ransomware attacks by aggregating and analyzing log data from various sources. If the same events are flagged to a single user and happen over a certain time range, it could indicate an activity that deserves more detailed attention from the organization.
4. User Behavior Analytics (UBA)
When it comes to human activity, UBA tools analyze user behavior and create a baseline of normality. All other deviations from this serene baseline—traversing petabytes in the middle of the night or on holidays, for example—result in alerts.
Best Practices for Ransomware Prevention
Ultimately, as much focus should be put on prevention as on detection. Here are the best practices to reduce risks associated with ransomware
1. Regular Backups
Protecting critical data from ransomware attacks is crucial through a reliable backup strategy. One strategy should be to backup frequently (daily or weekly) to maintain fresh data. These backups need to be stored offline, ideally in a different network, so they cannot be encrypted as part of an attack. Lastly, test and then re-test your backups for integrity and accessibility to ensure they can be restored when needed.
2. User Training and Awareness
Training workers about the dangers of phishing and safe browsing is essential for cybersecurity. Regular training can help users spot suspicious emails and avoid risky behaviors. With real-life examples and advice on how to validate sources, building up an awareness culture can dramatically mitigate the risks of phishing attacks and improve overall defenses in a rapidly evolving digital world.
3. Software Updates and Patch Management
Using all software, system, and application updates to maintain cybersecurity is necessary. Cybercriminals often strike by relying on known vulnerabilities for outdated systems, so the patching process absolutely needs to be done in a timely manner. Perform regular updates as much as possible to ensure all essential functions are optimized and, more importantly, that any security gaps that could give attackers entry into the system are closed. Prioritizing these updates will go a long way in reducing exposure to a ransomware attack and related threats.
4. Network Segmentation
You should segment your network as much as possible, propagating possible encrypted attacks to other networks. When critical systems and sensitive data are isolated from the rest of your environment, you can help contain incidents and limit impact.
5. Least Privilege Principle
It is the idea of the principle of least privilege, where users are given as little access as possible to do their jobs. This reduces the potential for ransomware.
Implement the principle of least privilege, ensuring users have only the access necessary to perform their jobs. This minimizes the potential attack surface for ransomware.
Incident Response Planning
No organization is completely immune to ransomware attacks, even with the best prevention strategies. A good incident response plan can be a game changer. The critical components of an incident response plan are as follows:
- Identification: Create detailed guidance on identifying and communicating possible ransomware events.
- Containment: Establish how to segregate compromised systems and control ransomware proliferation.
- Eradication: Detail the process of removing the ransomware from all affected systems and bringing everything back into standard working order.
- Recovery: Strategy that plans for data restoration from backups and system recovery.
- Post-Incident Review: Examine the incident for lessons and means to improve future defenses.
Conclusion
Given the ever-evolving nature of ransomware threats, proactive detection and prevention solutions have never been so critical to survival. By understanding the ransomware lifecycle, detecting in advance, leveraging more advanced detection techniques, and following best practices, organizations can significantly increase their cyber defense against these forms of attacks. After all, the idea is not just to catch ransomware but also to create a resilient cybersecurity posture for every attack, present and future.
Explore The Brand Hopper for more content
To read more content like this, subscribe to our newsletter