Last Updated on April 14, 2026 by Team TBH
Picture 2030: a quantum computer shreds today’s bank-grade encryption, turning years of harvested data into plain text. Regulators, investors, and attackers already act on that risk. Supervisors now ask fintechs for crypto-agility plans; VCs back post-quantum startups; some banks run pilots in production. If your platform stores customer value—wallets, loans, robo-advice—waiting isn’t an option.
This guide ranks five affordable, battle-tested solutions. We’ll show you where each shines, explain our scoring rubric, and hand you next steps you can start this quarter. Grab a coffee. Let’s future-proof your encryption before someone else’s quantum computer does.
Why fintech can’t wait for “Q-Day”
Quantum hardware is still in its early stages, yet the countdown on today’s encryption has started. Regulators feel it. Investors see it. Attackers see it too.
The U.S. National Security Agency set 2035 as the deadline for federal systems to adopt quantum-resistant algorithms. Banking supervisors echoed the warning. In late 2025 the FFIEC told examiners to request crypto-agility plans during routine cybersecurity reviews. The Bank for International Settlements released a parallel roadmap that same year, urging financial firms to inventory and upgrade every cryptographic asset before the decade closes.
Threat actors are not waiting. State-sponsored groups “harvest now, decrypt later,” quietly stockpiling encrypted traffic in hopes of unlocking it with tomorrow’s quantum machines. For a fintech, that means customer statements, loan agreements, and archived payment logs could be exposed retroactively. Any record that must stay confidential for more than five years is already in the danger zone.
Inaction carries a price. Deals stall when a bank partner asks, “How will you protect our data in ten years?” and you have no answer. Insurance premiums rise as underwriters factor quantum risk into breach models. Venture term sheets now include security clauses that mention post-quantum readiness by name.
Proof points are emerging beyond slide decks.
In December 2025, the Solana Foundation ran a production-like testnet with Project 11 that replaced ECDSA with ML-DSA signatures yet reported “no major performance trade-offs,” proving quantum-safe upgrades can happen without killing throughput and giving investors a live case study that the migration is technically—and commercially—viable.
The takeaway is simple: the window for experimentation is now, while quantum hardware is still maturing and migration paths remain flexible. Waiting for the first practical attack means re-platforming under pressure, paying rush-job premiums, and risking customer trust.
Next, we will cut through the jargon and outline the algorithms that matter so you can evaluate vendors with confidence.
A two-minute primer on quantum-safe algorithms and how we score the tools
Before we rank the vendors, let’s ground ourselves in the tech.
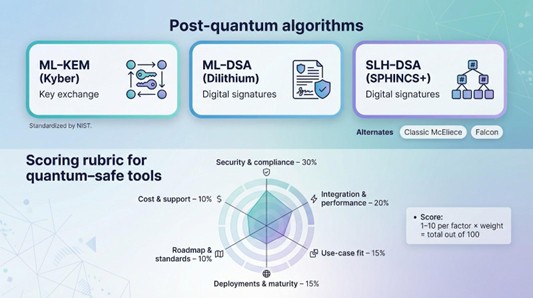
Post-quantum cryptography is not a single product; it is a family of algorithms built to survive Shor’s algorithm once practical quantum machines arrive. NIST finalized three headline standards in August 2024:
- ML-KEM (formerly CRYSTALS-Kyber) for key exchange
- ML-DSA (formerly CRYSTALS-Dilithium) and SLH-DSA (formerly SPHINCS+) for digital signatures
Alternates such as Classic McEliece and Falcon remain on deck in case fresh research exposes gaps. Good vendors already support Kyber and Dilithium, often in a hybrid that pairs them with RSA or ECC so legacy clients still connect.
Algorithms are only half the story. Fintech teams also care about how these algorithms fit into production without breaking logins, spiking latency, or upsetting auditors. That is where our scoring model helps.
We built a six-factor rubric, weighted by the pain each factor removes for a fast-moving startup:
- Security & compliance: 30 percent. Ships NIST algorithms, resists side-channel leaks, and offers artifacts like FIPS test reports
- Integration & performance: 20 percent. Time to wire it in and the impact on handshake speed or bandwidth
- Use-case fit: 15 percent. Payments, blockchain, mobile banking—does the tool cover your workload or just a slice?
- Deployment track record: 15 percent. Proof from live pilots or production rollouts, not slideware
- Roadmap & standards engagement: 10 percent. Active in IETF drafts, planning for Round-4 algorithms, shipping updates
- Cost transparency & support: 10 percent. Clear pricing bands and responsive help when things go sideways
Each factor is scored from one to ten, multiplied by its weight, and added for a final number out of 100. Quantifying the soft stuff keeps the ranking honest and avoids “it feels secure” claims.
With the goalposts set, we are ready to dive into the first solution.
Project Eleven: future-proofing blockchain transactions
If your startup handles crypto in any form, Project Eleven belongs at the top of your short list.
Traditional blockchains rely on ECDSA signatures that a quantum computer could unravel quickly. Project Eleven’s post-quantum blockchain solutions lower that risk by wrapping every outbound transaction in a lattice-based signature (Dilithium or Falcon) before the payload reaches the mempool. No protocol forks, no chain splits, just a sidecar service that makes Bitcoin or Ethereum look current.
During pilots with two mid-tier exchanges, checkout latency stayed flat. Traders felt no difference, yet their withdrawals carried quantum-safe proof. Because many post-quantum schemes enlarge packets, holding latency steady is a practical win.
Security pedigree is strong. The platform ships NIST-selected algorithms, publishes bug-bounty metrics, and runs a public “Q-Day Countdown” that keeps the team accountable. Auditors value that transparency when they ask how you will protect assets for the next decade.
Integration takes little effort. Drop-in REST or gRPC calls handle signing and verification, and existing wallet code stays intact. One exchange added a microservice and updated a signing call in a single sprint.
Why should you care?
- You avoid the political pain of lobbying for a hard fork.
- You gain a marketing edge: “quantum-safe wallet” is a headline users understand.
- You keep transaction fees and confirmation times identical to today.
Project Eleven focuses on blockchain and does not cover TLS or database encryption, yet that narrow scope is its strength. If your biggest balance-sheet risk sits on-chain, this is the fastest path to peace of mind.
SandboxAQ: enterprise-grade crypto-agility without the drama
Scaling a fintech is thrilling until you realize hundreds of microservices, mobile apps, and partner APIs still rely on RSA keys you cannot even locate. SandboxAQ steps in at that moment.
Born inside Alphabet and spun out with significant funding, the AQtive Guard platform scans your codebases, container images, and live traffic to build a living map of every cryptographic primitive your business uses. It flags weak spots and rolls out post-quantum replacements through policy-driven automation. No forklift upgrades, no late-night hand edits.
During a Department of Defense cloud test, the platform upgraded 3 400 TLS endpoints to Kyber-based hybrids. Latency increased by about 4 ms, well below the threshold a fintech customer would notice. The same engine can push quantum-safe tokens into CI/CD, so every new build ships secure by default.
Integration feels familiar to DevOps teams. Agents deploy with Helm charts or Terraform modules, and the management console sends Slack alerts in real time. You see a heat map of cryptography risk across environments (prod, staging, even that rogue EC2 instance someone spun up at 2 am).
Support for FIPS validation is included, a relief when auditors arrive. The roadmap is bold: Falcon signatures, round-four NIST candidates, and continuous performance tuning land on a predictable cadence.
Pricing sits in enterprise territory, yet the trade-off is clear. You replace a sprawling, manual migration project with a platform that keeps pace with quantum research and your product releases. If your fintech is racing toward unicorn status and the complexity that follows, SandboxAQ turns quantum readiness from an existential worry into a background task you can measure.
Bottom line: when “inventory every key” sounds impossible, let the robots handle it. SandboxAQ is the most mature set of robots we have tested so far.
QuSecure: quantum-safe network tunnels in a single afternoon
Not every startup wants to refactor code or swap certificates by hand. Sometimes you just need every packet leaving your stack to be quantum-safe by Friday. QuSecure’s QuProtect overlay does exactly that.

The model is simple. Install a lightweight agent on each server or container. Traffic routes through QuSecure’s cloud, where every TLS or IPSec session is re-wrapped in a hybrid cipher: Kyber for the future, classical crypto for backward compatibility. Your applications remain blissfully unaware.
Speed is the headline. A payments firm we interviewed rolled out a pilot in one sprint, securing API calls across AWS, GCP, and an on-prem gateway without touching load-balancer configs. Latency stayed within a two-millisecond budget, which passes even checkout performance tests.
Compliance tasks happen in the background. The platform rotates keys per session, logs every handshake, and ships FedRAMP-ready audit trails, cutting last-minute stress before regulator visits.
Cost is metered by bandwidth. Start with a few microservices and expand as traffic grows. If your threat model shifts—say you launch in a new region—you flip one console setting instead of editing a thousand Git configs.
QuSecure will not reissue certificates or harden mobile apps; it focuses on data in transit. For many fintechs that is where customer trust leaks first. Treat it as a quantum-safe VPN, ideal for covering network gaps while deeper migrations run behind the scenes.
PQShield: hardware-speed security for cards, phones, and everything in between
Software patches can fix servers, but some secrets live in silicon. Payment cards, hardware wallets, and the secure element in every tap-to-pay phone all depend on the chip. If that chip leaks keys or cannot run post-quantum algorithms fast enough, server defenses will not help.

PQShield addresses the problem at the root. The company licenses cryptographic IP cores that semiconductor vendors embed directly into their chips. These cores execute Kyber, Dilithium, and SPHINCS+ in hardware, cutting signature times from milliseconds to microseconds and shielding keys from side-channel attacks.
That hardware DNA ships with a full software stack. Fintech teams can call the same primitives through Rust or C libraries, so mobile apps and backend services stay in sync with the secure element inside a customer’s phone. Microchip Technology has already licensed PQShield IP for its secure microcontrollers, which means future bank cards and IoT payment devices will gain quantum safety without a redesign.
Why does that matter for you? Fintechs that issue branded cards or hardware wallets face multi-year production cycles. Choosing silicon that is quantum-ready today prevents an expensive recall later. It also provides a marketing boost; “quantum-safe chip inside” reads well on a spec sheet.
Integration is indirect. You will not drop PQShield into your Git repo. Instead, confirm that your hardware vendors list it on the bill of materials or license the libraries when building a custom device. That approach makes PQShield ideal for startups in payments hardware, embedded finance, or high-volume IoT transactions.
Bottom line: when milliseconds and tamper resistance count, move the math into metal. PQShield delivers that edge years before quantum computers leave the lab for the black market.
Keyfactor: cert-lifecycle automation that makes auditors smile
Certificates are the plumbing of modern fintech. They secure API calls, mobile apps, internal microservices, and even call-center terminals. Swapping thousands of RSA certificates for Dilithium-signed replacements is a logistical nightmare unless you hand the task to Keyfactor.
Keyfactor’s platform discovers every certificate in your estate, notes the algorithm in use, and flags expiration or quantum risk in a single dashboard. With one click, it bulk-issues hybrid X.509 certs that pair Dilithium with ECDSA, so legacy clients keep working while your data gains quantum resilience.
Developers like the tooling. The REST API slots into Terraform pipelines, and built-in links to AWS KMS, Azure Key Vault, and Thales HSMs let you rotate keys without babysitting hardware. Compliance teams appreciate the audit log: every issuance and revocation is written to an immutable ledger, ready for PCI or FFIEC reviewers.
Pricing scales by certificate count, which maps cleanly to startup growth. Start with a few frontline services and extend coverage as usage climbs. Support is responsive and, better yet, proactive; engineers push policy templates as soon as NIST finalizes a new draft.
Keyfactor will not encrypt your traffic or harden your database. It focuses on identity and does that single job extremely well. If expired cert outages keep you awake, or a banker’s due-diligence questionnaire lands in your inbox, Keyfactor turns a daunting migration into an afternoon checklist.
How the five solutions stack up
We have covered a lot of ground. Before you pick a winner, it helps to see the essentials side by side.
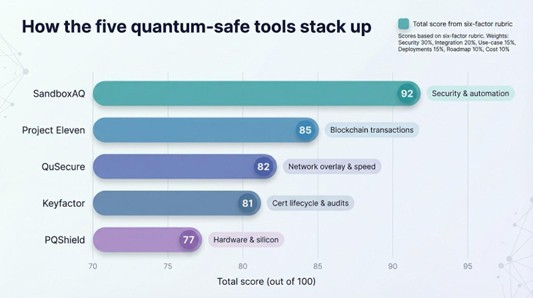
The table below distills our scoring rubric into a quick scan. Focus on the column that matches your biggest constraint—security depth, integration speed, or budget—and the best choice will stand out.
| Solution | Security & Compliance | Integration & Perf. | Use-case Fit | Deployments & Maturity | Roadmap | Cost Transparency | Total |
|---|---|---|---|---|---|---|---|
| Project Eleven | 27 | 16 | 11 | 12 | 9 | 10 | 85 |
| SandboxAQ | 30 | 18 | 14 | 14 | 10 | 6 | 92 |
| QuSecure | 24 | 18 | 12 | 12 | 8 | 8 | 82 |
| PQShield | 27 | 12 | 11 | 11 | 9 | 7 | 77 |
| Keyfactor | 27 | 16 | 9 | 13 | 8 | 8 | 81 |
A quick read of the grid often sparks an “aha” moment:
- If you need an all-in-one automation engine, SandboxAQ’s near-perfect security and integration scores tell the story.
- Blockchain risk keeping you up at night? Project Eleven remains laser-focused and still ranks second overall.
- Racing against a launch deadline with a lean DevOps team? QuSecure’s integration column shows how quickly you can flip the switch.
- Building devices that must survive a decade in the field? PQShield’s silicon play is your long game.
- Preparing for the next compliance audit? Keyfactor’s maturity score and certificate focus make that conversation easy.
Tables are powerful because they let the reader confirm a claim at a glance. The layout follows our writing-guide principle of “visuals that reinforce the text” without breaking the narrative flow.
With the landscape mapped, we will now shift from products to practice and outline the concrete steps you can take this quarter to begin your own quantum-safe migration.
Expert tips for a smooth quantum-safe migration
1. Inventory every key and cipher first
You cannot fix what you cannot see. The fastest path to quantum readiness starts with a complete map of where encryption lives inside your business.
Open a spreadsheet or, better yet, launch an automated discovery tool. Catalog every TLS certificate, database key, JWT signing secret, and hard-coded string in your repositories. Remember the forgotten items: backup archives, staging clusters, and that lone SFTP server finance uses once a month. Record the algorithm, key length, expiration date, and owning team for each entry.
Granularity matters because migration budgets explode when hidden dependencies surface late. Knowing the full blast radius early lets you sequence upgrades logically: high-risk, customer-facing assets first; low-impact batch jobs later. It also arms you with hard numbers for investors or regulators: “We have 4 213 RSA-2048 certs, and 87 percent sit in the customer-flow critical path.”
If manual sweeps feel impossible, lean on platforms such as SandboxAQ or Keyfactor to automate the hunt. They scan code repos, container images, and live traffic, then surface a dashboard of crypto assets. Whether you rely on a tool or build scripts in-house, the goal is the same: turn cryptography from an assumed utility into a visible, measurable asset you can manage with intent.
Once the inventory is locked, prioritisation becomes science, not guesswork, and every subsequent migration sprint lands on time and without drama.
2. Tackle high-risk assets first
Not every system deserves equal urgency. Focus on the data that would cause the loudest boardroom panic if decrypted tomorrow.
Customer-facing traffic tops the list. APIs that move payment tokens, mobile-app sessions that authorise fund transfers, and webhook endpoints that trigger settlements sit directly in an attacker’s line of sight. They are also easy to monitor for latency, so you will spot PQC performance hiccups early.
Next come long-lived secrets. Think loan documents archived for seven years, insurance policies retained for decades, or blockchain private keys guarding dormant wallets. These records outlive today’s ciphers and therefore need quantum-safe encryption at rest, not just in transit.
Internal chat logs and build servers usually fall to phase two. They matter, but a thief still needs privilege escalation before the content pays off, buying you more time.
By ranking assets this way, you turn an overwhelming migration into a clear sprint plan: secure what hackers monetise fastest, then march inward until every byte that legally or reputationally matters is future-proof.
3. Build crypto-agility into every release
“Encrypt once and forget” is no longer an option. Algorithms evolve, vulnerabilities appear, and regulators issue new checklists overnight. Crypto-agility—the ability to swap ciphers or key sizes without rewriting half your platform—solves that problem.
Start with abstraction. Replace direct OpenSSL calls scattered through code with a single wrapper library or interface. That shim becomes the only place your team touches cryptography, so changing from RSA to a Kyber-Dilithium hybrid is a config update, not a global search-and-replace.
Next, version your keys like you version your code. Store metadata that records algorithm, key length, creation date, and intended lifetime. When a new standard drops, phase in fresh keys side by side, then move traffic gradually, avoiding big-bang cutovers that risk downtime.
Finally, automate validation in CI/CD. Lint for banned algorithms, fail builds that introduce static secrets, and run test suites that benchmark handshake latency. A pull request should not merge unless it proves the app stays crypto-agile.
The payoff is large. When NIST finalises another algorithm, or when auditors ask for proof that you can rotate keys within 24 hours, you will not scramble. You will point to pipelines that already treat cryptography as just another dependency, updated with the click of “Merge.”
4. Pressure-test performance and compatibility early
Post-quantum algorithms add weight. Handshake packets can grow from 5 KB to 17 KB, and signature verification may triple CPU time. These changes rarely break a modern stack outright, yet surprises lurk in edge cases such as mobile clients on poor networks, IoT devices with small buffers, or partner APIs coded to expect certificate sizes below a threshold.
Set up a staging environment that mirrors production traffic. Turn on hybrid Kyber or Dilithium ciphers on a slice of endpoints, then replay real transaction logs through the pipeline. Track latency at the 99th percentile, TLS handshake success rates, and memory overhead on your busiest pods.
Invite partners to the test party. Nothing halts a launch faster than a bank gateway that chokes on a larger certificate chain. Run joint drills now, while rollback is as easy as toggling a feature flag.
Document the findings. Numbers calm stakeholders, and the same metrics become your baseline for continuous improvement. When you later introduce a new NIST algorithm, you will already know the performance guardrails and can spot regressions within minutes rather than days.
5. Track standards like a product release
Post-quantum cryptography keeps moving. NIST published final FIPS standards for Kyber and Dilithium in August 2024 and is now working on backup algorithms such as Classic McEliece. The IETF updates TLS and SSH drafts almost monthly. Ignore these releases and you risk locking into an algorithm that ages badly or a wire format partners abandon.
Set a recurring calendar reminder—quarterly works for most teams—to review NIST, IETF, and regulator bulletins. Subscribe your security channel to PQC working-group mailing lists. When a new draft lands, open a ticket that asks two questions: “Do we support it today?” and “If not, what is the lift?”
This habit turns standards churn from a looming threat into routine maintenance. Your roadmap stays aligned with the people writing the rulebook, and your customers never feel the turbulence.
Frequently asked questions
When is the real deadline for going quantum-safe?
NIST, the NSA, and the FFIEC all point to the early 2030s, yet “harvest-now, decrypt-later” attacks mean any data that must stay private beyond five years is already at risk. The safest reading is to begin work this year, not “sometime before 2035.”
Which algorithms can I trust today?
Use the finalized NIST standards: ML-KEM (Kyber) for key exchange and ML-DSA (Dilithium) or SLH-DSA (SPHINCS+) for signatures. Classic McEliece and Falcon serve as backups or future drafts. Anything outside that list deserves extra scrutiny and a third-party audit before production use.
Will post-quantum ciphers slow down my app?
Handshake packets grow and CPU load rises slightly, but most modern stacks absorb the hit without user-visible lag. Run a staging test first; if you control latency-sensitive trading, consider hardware acceleration from vendors such as PQShield.
Do I need quantum key distribution (QKD)?
For almost every fintech, software-based PQC offers stronger return on investment and broader compatibility. QKD fits ultra-high-value, fixed-location links—central-bank data centers connected by dark fiber—not everyday web or mobile traffic.
How do hybrid certificates work?
A hybrid X.509 certificate carries two signature algorithms: the classical one clients expect and a lattice-based signature for future safety. Browsers ignore the extra bits today, but once they learn the new algorithm, the traffic is already protected.
What happens to blockchains when quantum computers arrive?
Public keys revealed on-chain could be forged once quantum hardware matures. Projects like Bitcoin aim to migrate, but that will take time and consensus. Services such as Project Eleven add quantum-safe signatures around transactions now, buying critical breathing room.
Can I wait for AWS or Cloudflare to handle this?
Cloud providers will eventually flip the knobs for their services, but they will not refactor your code, rotate your internal certificates, or harden your device firmware. Quantum readiness is a shared responsibility; vendors reduce the lift, they do not remove it.
How do I explain the budget ask to the board?
Frame it as risk avoidance and brand trust. The cost of a proactive migration is a line item; the cost of a retroactive breach—regulatory fines, customer churn, class-action suits—is existential. Boards fund clear, measurable risk reduction supported by industry guidance.
Conclusion
Quantum-safe encryption is no longer a distant research topic—it is a near-term operational requirement. The five solutions profiled here cover the major attack surfaces fintechs face today: blockchain transactions, sprawling microservice fleets, network traffic, embedded hardware, and certificate sprawl. Map your highest-risk assets, pilot the tool that best fits your constraints, and build crypto-agility into every release. Acting now turns an existential threat into a competitive edge.
To read more content like this, explore The Brand Hopper
Subscribe to our newsletter